Integer Overflow Vulnerability: The Hidden Bug behind the Crash

In the world of software development, we often focus on obvious threats like SQL injection or cross-site scripting. However, lurking beneath the surface, a more subtle yet equally dangerous vulnerability exists, known as Integer Overflow. This seemingly innocuous issue can lead to application crashes, unexpected behaviour, and even security breaches if not properly addressed.
The Problem: When Numbers Exceed Their Limits
An integer overflow occurs when an arithmetic operation attempts to create a numeric value that is outside the representable range for the integer type. Imagine trying to pour five litres of water into a four-litre bottle it simply overflows.
In programming, when an integer overflows, the result wraps around to the other end of the range. For example, if a 32-bit unsigned integer (ranging from 0 to 4,294,967,295) reaches its maximum value and you add 1 to it, instead of resulting in 4,294,967,296, it will wrap around to 0.
Why is this a Vulnerability?
While this wrapping behaviour might seem like a quirky technical detail, it can have serious consequences in application security:
- Application Crashes and Unexpected Behaviour: If a critical part of the application relies on the accurate value of an overflowing integer, the unexpected wrap-around can lead to logical errors, incorrect calculations, and ultimately, application crashes.
- Memory Corruption: In some cases, an integer overflow can be exploited to write data outside of intended memory buffers. For instance, if an integer overflow affects the calculation of a buffer size, an attacker might be able to write beyond the allocated memory, potentially overwriting critical data or injecting malicious code.
- Security Bypass: Integer overflows can be leveraged to bypass security checks. Imagine a scenario where a system checks the length of user input against a maximum value stored as an integer. If an attacker can manipulate this length calculation to cause an integer overflow, the check might incorrectly report a small, valid length, allowing them to send much larger, potentially malicious input.
- SQL Injection (Indirectly): As you might have seen in the image examples, integer overflows can sometimes indirectly lead to SQL injection vulnerabilities. For example, if an integer overflow affects a value used in constructing a SQL query (like a length parameter), it might allow an attacker to manipulate the query in unintended ways.
A Real-World Scenario: Integer Overflow to SQL Error and Application Crash
Let's consider a practical example that demonstrates how an integer overflow can lead to a critical application failure.
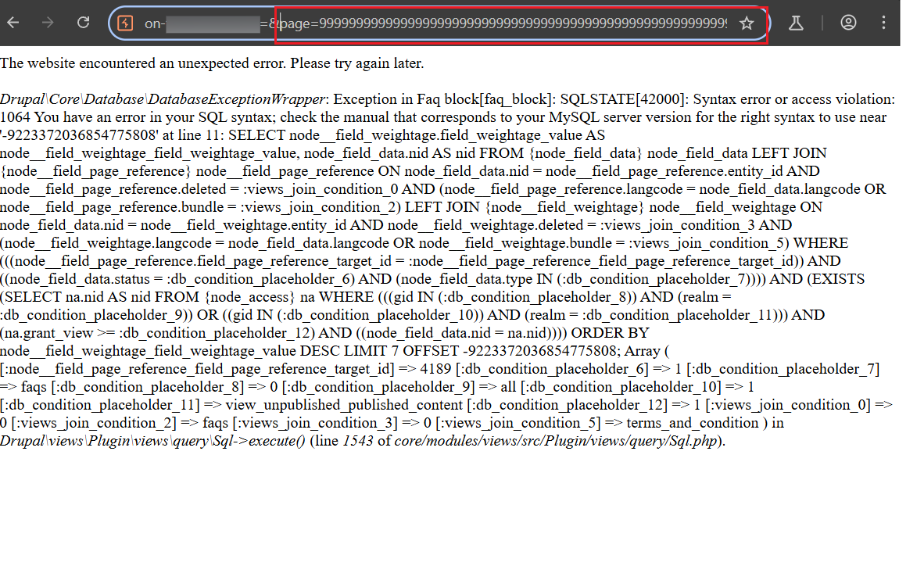
Imagine browse a website with a pagination feature, where the URL contains a page parameter. Here, the page=2 parameter tells the server to fetch the second page of content. This page value is likely processed by the backend, perhaps to calculate an OFFSET in a database query, determining which records to retrieve.

Now, what happens if an attacker decides to test the limits of this parameter by supplying an extraordinarily large number?
By changing page=2 to a ridiculously large number, the intent is to trigger an integer overflow. The application likely expects the page parameter to fit within a standard integer type (e.g., a 32-bit or 64-bit signed integer). When such a massive number is provided, it exceeds the maximum capacity of the integer variable used to store it.

The Catastrophic Response: Integer Overflow to SQL Error
The server's response to this modified request clearly illustrates the impact
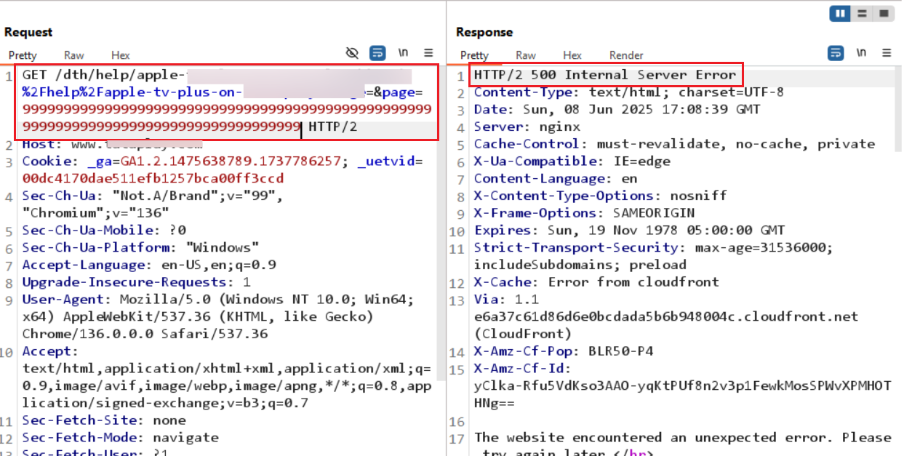
Let's dissect this crucial response:
- HTTP/2 500 Internal Server Error: This immediately tells us the application has crashed or encountered a severe unhandled error.
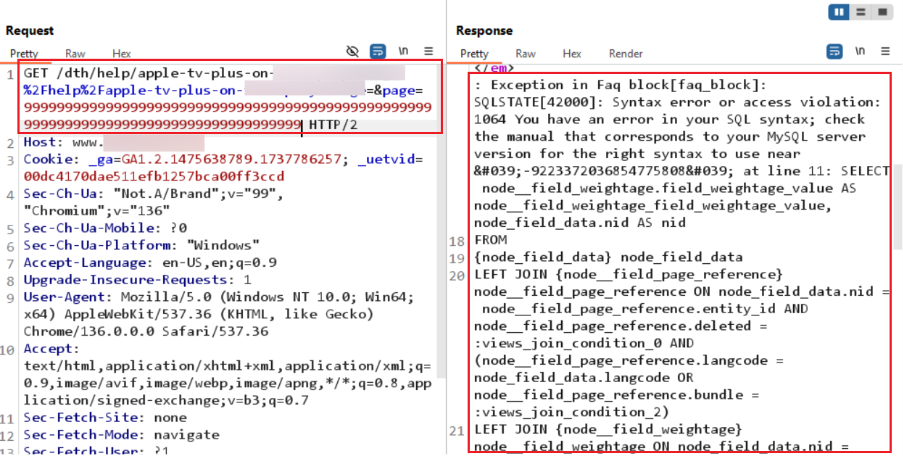
- SQLSTATE[42000]: Syntax error or access violation: 1064 You have an error in your SQL syntax: This is the smoking gun! The application is revealing a SQL error.
- LIMIT 7 OFFSET -9223372036854775808;: This is the most telling part. The extremely large number provided in the page parameter has, due to an integer overflow, been converted into a negative value: -9223372036854775808. This is the minimum value a 64-bit signed integer can hold, a classic sign of an overflow where the number "wrapped around."
The database (MySQL, indicated by 1064 You have an error in your SQL syntax) then receives a query with an invalid negative OFFSET value. Database systems typically expect a positive or zero OFFSET for pagination. This leads to a Syntax error or access violation, causing the SQL query to fail, and consequently, the application (Drupal in this case, as indicated by the stack trace) crashes, exposing debugging information in the error message.
The Security Implications of This Scenario:
This specific example demonstrates multiple security issues stemming from a single integer overflow:
- Denial of Service (DoS): By simply manipulating a URL parameter, an attacker can crash the application, making it unavailable to legitimate users. This is a direct DoS attack.
- Information Disclosure: The detailed error message, including the full SQL query, database type (MySQL), and parts of the application's internal structure (Drupal, core modules, file paths), provides valuable reconnaissance information to an attacker. This data can be used to craft further, more sophisticated attacks.
- Potential for Further Exploitation: While this example shows a crash, in other contexts, an integer overflow leading to an invalid SQL parameter might be subtly manipulated to perform SQL injection if the application doesn't properly sanitize or parameterize the resulting (overflowed) value.
How to prevent Integer Overflow Vulnerabilities?
The good news is that integer overflow vulnerabilities can be mitigated with careful coding practices:
- Implement Robust Input Validation: Always validate all user inputs, especially numerical parameters in URLs, forms, and API requests. Ensure they fall within the expected, sensible range before any processing. For page numbers, for example, define a clear maximum.
- Perform Explicit Range Checks: Before performing operations that could potentially lead to an overflow (like calculating offsets from page numbers), explicitly check if the result will exceed the maximum or minimum value of the integer type you are using.
- Utilize Appropriate Data Types: Choose integer types (e.g., long long in C++, Big Integer in Java, or appropriate database integer types) that can safely accommodate the largest anticipated values. If your application might deal with extremely large numbers that exceed standard integer limits, consider using libraries or custom implementations for arbitrary-precision arithmetic.
- Database Query Parameterization: Always use parameterized queries (prepared statements) for database interactions. This separates the SQL code from the data, preventing syntax errors from malicious input and making it harder for overflowed values to directly manipulate the query structure.
- Error Handling and Logging (Without Disclosure): Implement robust error handling that catches exceptions gracefully. Instead of displaying detailed error messages to users, log them securely on the server side for debugging and present a generic, user-friendly error message.
How AuthenticOne Can Help with Integer Overflow Vulnerabilities?
AuthenticOne identifies and mitigates integer overflow vulnerabilities before attackers can exploit them by continuously testing application behaviour at runtime.
When an unusually large or negative value is input whether during testing or normal use, AuthenticOne inspects how the application processes it. If the value causes an unexpected result, such as numeric wraparound, negative memory allocation, or logic bypass, it is immediately flagged as a potential overflow.
AuthenticOne then generates detailed alerts for developers, showing the exact input, code location, and impact, allowing for quick remediation.
Additionally, it can block the operation in real time to prevent exploitation. By proactively detecting unsafe arithmetic behaviour and enforcing input validation policies, AuthenticOne ensures vulnerabilities like integer overflows are caught and mitigated early long before an attacker has a chance to exploit them.
Conclusion:
The case study of the page parameter clearly illustrates that integer overflows are not just theoretical concepts or vulnerabilities confined to controlled lab environments. This specific instance, discovered in a live, publicly accessible Target, proves they are real, exploitable weaknesses that can be triggered in production systems, leading to immediate and severe consequences, including application unavailability and sensitive information disclosure.
By understanding the mechanics of integer overflows and implementing robust preventative measures – especially rigorous input validation and careful handling of numerical data, particularly when interacting with databases – developers can build more secure and reliable applications. Paying attention to the seemingly small details, like the limits of integer types, can make a big difference in the overall security posture of your software.
Advisory & Compliance Services
Audit & Assessment Services
Managed Security Services
Governance & Compliance Framework Development
Cyber Key Performance IndicatorsCISO Advisory
Advisory and Compliance ServicesStandard & Regulatory AdvisoryBusiness Continuity & Disaster Recovery PlanningIncident Response ReadinessData Privacy
Audit and Assessment Services
Cloud Security Assessment
Cyber Maturity Assessment
Privacy Impact Assessment
Red Teaming Service
VAPT
Managed Security Services
SOC as a Service
Third Party Risk Management
Vulnerability Management Services