Supply Chain Security: Frameworks, Standards, Regulations and Best Practices

In today's highly interconnected world, securing the supply chain has become more critical than ever. As businesses increasingly rely on global networks, the potential for disruptions, cyberattacks, and fraud has grown exponentially. The complexity of modern supply chains—spanning across multiple industries, countries, and partners—creates a landscape that is both dynamic and vulnerable.
This blog explores the various frameworks, standards and regulations designed to address these challenges, while offering best practices that organizations can adopt to minimize risk. Whether you're in manufacturing, logistics, or retail, securing your supply chain is not only about mitigating threats but also building trust with your customers and partners.
In the following sections, we will delve into the frameworks, standards and the regulatory landscape that help fortify the backbone of your business operations.
Section A: Supply Chain Security Frameworks
A supply chain security framework is a structured approach to managing and mitigating risks associated with the supply chain. It involves identifying, assessing, and addressing potential threats to ensure the integrity, security, quality, and resilience of the supply chain, its products and services.
Common Supply Chain Security Frameworks
1. Supply Chain Levels for Software Artifacts (SLSA)
SLSA, pronounced "salsa," is a security framework designed to safeguard the integrity of software supply chains. It provides a checklist of standards and controls to prevent tampering, improve integrity, and secure software packages and infrastructure.
SLSA defines four levels of assurance. Each of them represents a progressively stronger security posture. They are:
| Levels | Description | Benefits |
| 1 | Indicate whether the build is scripted or automated | A] Basic code source identification B] Vulnerability Management |
| 2 | Requires version control and a hosted build service to generate provenance | A] Gain a level of trust in tamper prevention |
| 3 | Requires that source and build platforms conform to specific standard | A] Enables auditing B] Ensures provenance integrity C]Organizations can rely on auditors’ certification |
| 4 | Requires two-person review for all changes | A] Comprehensive security B] It is reproducible |
In summary, SLSA offers a clear progression from basic provenance to top-level security, ensuring software is trustworthy and resilient. Adopting SLSA benefits producers, consumers, and infrastructure providers alike.
2. Secure Supply Chain Consumption Framework (S2C2F)
The Secure Supply Chain Consumption Framework (S2C2F) is a framework developed by Microsoft in collaboration with the Open-Source Security Foundation (Open SSF). It aims to secure the ingestion of open-source software (OSS) into an organization's development process.
S2C2F includes a set of eight practices. They are:
| Practice | Description |
| Ingest | Acquire OSS components securely. |
| Scan | Scan OSS for vulnerabilities continuously. |
| Inventory | Maintain an accurate inventory of all OSS components. |
| Update | Ensure OSS components are up to date |
| Audit | Audit OSS components for compliance and security regularly. |
| Enforce | Implement policies to enforce security standards. |
| Rebuild | Rebuild OSS components from source to ensure integrity. |
| Fix | Address vulnerabilities and issues promptly. |
In conclusion, the Secure Supply Chain Consumption Framework (S2C2F) offers multiple benefits. It enhances security and governance across the supply chain, while also speeding up vulnerability fixes. The framework ensures compliance with security standards and helps build trust among stakeholders, partners, and consumers, ultimately strengthening the resilience of the entire supply chain.
Section B: Supply Chain Security: Standards and Regulations
As supply chains become more complex, strong security standards and regulations are crucial for protecting both physical and digital assets.
Supply chain security standards are guidelines designed by the International Organization for Standardization (ISO), National Institute of Standards and Technology (NIST) and other International Bodies to protect the supply chain from various risks.
Supply chain security regulation refers to the policies, standards, and practices established by governments and organizations to protect supply chains from various threats.
Supply chain security standards and regulations play a vital role in safeguarding the integrity and resilience of supply chains. Below are key areas organizations should prioritize:
Supplier vetting and risk assessment:
Establishing incident response protocols and robust data protection measures helps in evaluating potential suppliers, leading to trustworthy partnership
Robust data security practices:
Following best practices like encryption, access controls, regular updates, and adhering to data protection regulations avoid penalties and build trust with partners
Tracking and monitoring of shipments:
Monitoring the goods in transit and ensuring that only authorized personnel have access to critical assets prevent theft, damage, and tampering
Compliance with import/export laws:
Adhering to industry-specific legal requirements help in maintaining operational resilience and avoiding legal complications
Implementing security measures:
Conducting third-party risk assessment and vendor compliance helps to quickly identify and address security issues within the supply chain
Regular audits and vulnerability assessments:
Reviewing and testing security weaknesses strengthens the supply chain’s resilience and helps in business continuity
Contingency plans for disruptions:
Preparing strategies to handle supply chain interruptions; collaborating with industry partners and staying updated on regulatory changes helps to have an adaptable supply chain
Appropriate employee training on security protocols:
Educating stakeholders and staff on best practices for security creates awareness and protects from insiders’ threats.
Common Supply Chain Security Standards
Here is a brief outlook on few widely recognized standards: ISO 28000, C-SCRM, and SCS 9001
1. International Organization for Standardization: ISO 28000
ISO 28000 is a standard specifically designed for supply chain security. It provides a framework for organizations to identify, assess, and mitigate potential threats across their entire supply chain operations: from raw materials to finished products delivery. It ensures the safety and integrity of goods throughout the logistics process.
Regardless of size or industry, any organization involved in a supply chain can implement ISO 28000 to improve their security posture. It allows organizations to prioritize mitigation strategies based on the severity of threats.
Benefits of Implementing ISO 28000
Figure 1: Benefits of ISO 28000
Relevance of ISO 28000 for sectors:
Logistics companies: Freight forwarders, third-party logistics providers, delivery companies
Manufacturing companies: Companies having complex supply chains that includes raw materials, finished goods, and distribution networks
Retailers: Companies managing large inventories and distribution centers
Pharmaceutical companies: Organizations handling sensitive medical supplies
High-value goods manufacturers: Companies producing expensive equipment or use technology requiring robust security measures
2. Cybersecurity Supply Chain Risk Management (C-SCRM)
The National Institute of Standards and Technology (NIST) provides guidelines and best practices to help organizations manage and mitigate cybersecurity risks throughout their supply chains.
It integrates cybersecurity supply chain risk management (C-SCRM) into overall risk management, including strategies, policies, and assessments. NIST emphasizes checking on the final products, their components, entire supply chain journey, and updates. The guidelines make operations more secure and resilient.
Benefits of Implementing Cybersecurity Supply Chain Risk Management
Figure 2: Benefits of C-SCRM
Relevance of C-SCRM for sectors:
It's primarily beneficial for all organizations with complex supply chains. The beneficiaries include IT security teams, decision makers, procurement teams, legal and compliance teams
3. Supply Chain Security (SCS)- 9001
SCS 9001 is the first global supply chain security standard for Information and Communication Technology (ICT). It ensures that service providers and manufacturers meet critical security benchmarks to reduce cybersecurity risks. This standard takes a holistic approach, covering design, development, production, delivery, installation, and maintenance of hardware, software, and services. It also includes performance-based measurements to assess the reliability and security performance of products and services.
The standard is unique as it is based on a Quality Management System (QMS), incorporating industry guidelines and best practices, such as ISO 27001, the Prague Proposals, relevant NIST standards, and the CSIS Criteria for Security and Trust.
Benefits of SCS-9001

Figure 3: Benefits of SCS 9001
Relevance of SCS 9001 for sectors:
SCS 9001 is specifically designed for the information and communications technology (ICT) industry, including software, hardware, and services that connect to global networks.
Common Supply Chain Security Regulations
Here is a brief outlook on some of the common Regulations: DORA, CRA, NIS2, GDPR, and EO14144.
4. The Digital Operational Resilience Act (DORA)
The Digital Operational Resilience Act (DORA) is a European Union (EU) regulation that aims to improve the cybersecurity resilience of financial institutions. It establishes stringent guidelines for digital operational resilience and is closely related to supply chain security.
DORA requires organizations to conduct thorough risk assessments of their third-party suppliers and vendors - IT service providers, data centers, and cloud solution providers. By incorporating TPRM practices into the supply chain security strategies, organizations can manage risks more effectively and ensure a robust and secure supply chain.
Benefits of DORA Compliance in Supply Chain Security

Figure 4: Impacts of DORA Regulation on Supply Chain Security
Relevance of DORA for sectors:
Financial institutions: Banks, investment firms, insurance companies, and other regulated entities
Third-party ICT providers: Companies providing critical IT services to financial institutions must comply with DORA standards
5. Network and Information Security 2 (NIS2)
The Network and Information Security 2 (NIS2) Directive enhances supply chain security in the EU by introducing strict cybersecurity measures. It ensures resilience by addressing supply chain security, mandating security measures, incident reporting, and uniform sanctions across the EU. By following NIS2 requirements, organizations can strengthen their supply chain security and manage risks more effectively.
Benefits of Network and Information Security 2 (NIS2)

Figure 5: NIS2 Impacts on Supply Chain Security
Relevance of NIS2 for Sectors:
Organizations in essential sectors: Food production, manufacturing, energy, healthcare, finance, transportation, and digital infrastructure providers.
6. The Cyber Resilience Act (CRA)
The Cyber Resilience Act (CRA) regulation was introduced by the European Union. It focuses on securing the software supply chain by imposing strict requirements on manufacturers and suppliers. It focuses to reduce vulnerabilities in digital products and thus mandates comprehensive assessment of third-party suppliers. It dictates to document every software component’s origin, version, and security status. Non-compliance with CRA will lead to fines and market exclusion.
Benefits of Cyber Resilience Act (CRA)

Figure 6: Benefits of CRA Regulation
Relevance of CRA for Sectors:
CRA primarily benefits manufacturers and software developers.
7. General Data Protection Regulation (GDPR) in Supply Chain Security
GDPR is highly related to supply chain security as organizations need to protect personal data throughout their supply chains. It includes data collected from suppliers, logistic partners, employees, contractors, and customers.
Organizations must have a legal basis for personal data collection, storage, and sharing. The concerned individuals must know how their data is used and protected from breaches and unauthorized access. Moreover, the organizations must report data breaches (if any) to relevant authorities and individuals.
Benefits of GDPR compliance in supply chain security

Figure 7: Benefits of GDPR Compliance in supply chain security
Relevance of GDPR for Sectors:
GDPR compliance is needed for every business that collects personal data from their suppliers, logistic partners, employees, contractors, and customers.
8. Executive Order 14144:
The directive EO 14144 aims to build upon previous initiatives, including Executive Order 14028. It introduces measures to secure the nation's digital infrastructure. With reference to supply chain security, the directive mandates agencies to integrate cybersecurity supply chain risk management programs into enterprise-wide risk management activities. Also, the Federal Government must establish a set of practical and effective security practices for software procurement.
The order also encourages the use of new technologies, promotes the adoption of quantum-resistant cryptography by 2030 to future-proof security. Additionally, it fosters public-private partnerships to strengthen cyber defense measures.
Benefits of EO 14144 Initiatives w.r.t. Supply Chain Security
Figure 8: Benefits of EO 14144 in Supply Chain Security
Relevance of EO 14144 for Sectors:
EO 14144 is relevant to federal agencies, software and cloud service providers, and industries such as transportation, healthcare, and finance.
Section C: Supply Chain Security Best Practices
The global supply chain market size is projected to grow from USD 2.52 billion in 2024 to USD 5.14 billion by 2030 at a Compound Annual Growth Rate CAGR 12.6% during the forecast period. The rising frequency of cyber-attacks on third-party networks, such as ransomware and phishing are a major driver of market expansion, pushing business to upgrade their security frameworks. (Source: MarketsandMarkets Research Pvt. Ltd ).
According to Statista, the annual number of customers impacted by supply chain attacks globally in 2024 is estimated to be 183,174 customers.
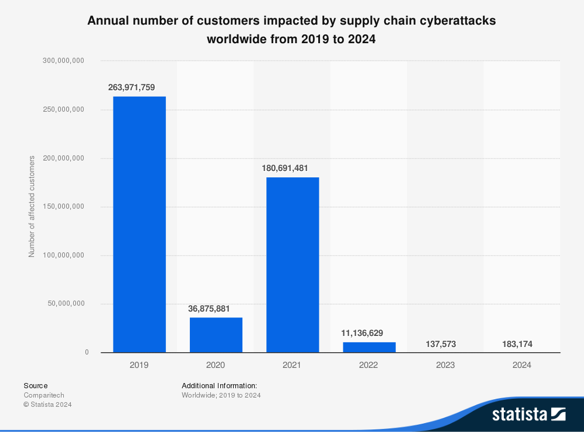
Fig 9: Annual number of customers impacted by supply chain attacks [Statista Report]
Relying on third-party vendors and suppliers introduces significant vulnerabilities. A single misstep by a partner can result in costly data breaches, compliance failures, or severe financial losses. Evidently, adopting best practices is essential for safeguarding against these risks. Following these practices not only enhances productivity, efficiency, and security but also ensures compliance, lowers costs, manages risks, boosts customer satisfaction, and strengthens your competitive edge.
Five critical supply chain security best practices are outlined below.
1. Adopting a strategic and integrated approach to supply chain security
Supply chain security isn't just an operational concern, it's a strategic imperative that must start from the highest levels of leadership. Set up a concrete and achievable goals that guarantees consistency and accountability throughout the entire process:
- Striving for zero security incidents within your supply network or attaining full compliance with all relevant regulations
- Integrating robust security practices into every facet of your supply chain operations—from sourcing and procurement to manufacturing and delivery
- Cultivating a culture where every employee recognizes their vital role in maintaining supply chain integrity to mitigate risks, enhance trust with suppliers, partners, and customers.
Adopting this integrated approach positions your organization to thrive amid uncertainty and evolving risks also.

Figure 10: Supply Chain Security Best Practice No.1
2. Managing Supply Chain Risks
Embracing the risk assessment process detailed in ISO 31000:2018 [refer add] helps you to systematically identify and mitigate vulnerabilities arising from dependencies on third-party suppliers and operating partners. Here's how:
- Identify Important IT and Operational Technology (OT) Supplier Dependencies: Identify IT and OT suppliers critical to your operations and understanding relationships. This allows you to evaluate the impact of disruptions and implement strategies to secure these essential links.
- Identify Important Customer Dependencies: Determine which customers are vital to your business success. This enables you to anticipate how changes in their operations might affect your supply chain and regulate accordingly.
- Map Critical Software Dependencies: Break down the software infrastructure to its granular level—packages, libraries, and modules. This detailed mapping uncovers hidden vulnerabilities and helps protect against supply chain attacks targeting software components.
- Identify Single Points of Failure and Other Essential Dependencies: Determine areas where a single malfunction could disrupt the entire operation. This helps to develop redundancies and contingency plans to improve resilience.
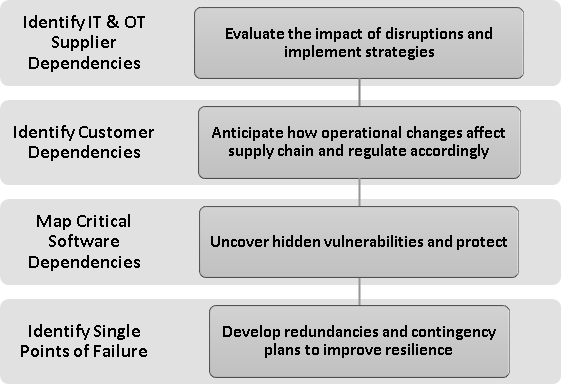
Figure 11: Supply Chain Security Best Practice No. 2
3. Managing supplier relationships
The best-practice standard for management of supplier relationships is as outlined in ISO/IEC 27001:2022 Chapters 5.19–5.23.
- The ISO 27001 standard defines ISO 27001 Annex A 5.19 as: Processes and procedures should be defined and implemented to manage the information security risks associated with the use of supplier’s products or services.
This ensures that you maintain an agreed level of information security in supplier relationships.
- The ISO 27001 standard defines ISO 27001 Annex A 5.20 as: Relevant information security requirements should be established and agreed with each supplier based on the type of supplier relationship.
This grants the organization the right to audit the supplier's compliance with security requirements.
- The ISO 27001 standard defines ISO 27001 Annex A 5.21 as: Processes and procedures should be defined and implemented to manage the information security risks associated with the ICT products and services supply chain.
This helps to update agreements and security policies to reflect any changes in services or risk profiles.
- The ISO 27001 standard defines ISO 27001 Annex A 5.22 as: The organization should regularly monitor, review, evaluate and manage change in supplier information security practices and service delivery.
This helps to establish procedures for reporting, investigating, and resolving security incidents involving suppliers.
- The ISO 27001 standard defines ISO 27001 Annex A 5.23 as: Processes for acquisition, use, management and exit from cloud services should be established in accordance with the organization's information security requirements.
This helps to understand the supplier's security practices and ensure that security requirements are reached at all levels of the supply chain.
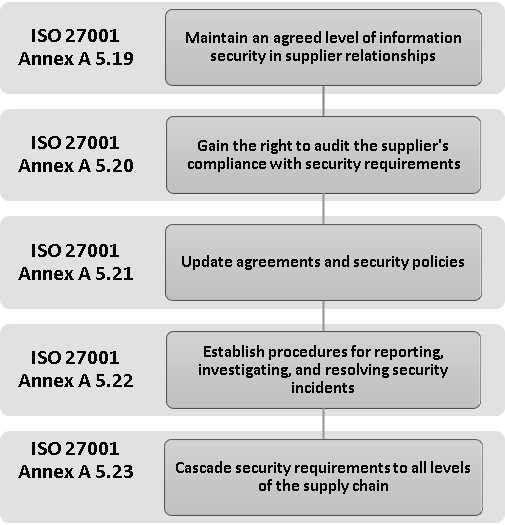
Figure 12: Supply Chain Security Best Practice No. 3
4. Handling Vulnerabilities Right
Vulnerabilities handled by suppliers lead to patches that must be applied to the product user’s network or infrastructure components. Remote products face even higher risks, emphasizing the need for a systematic vulnerability handling practice. Maintaining integrity throughout this process is paramount. This practice involves identifying, assessing, and proactively mitigating weaknesses within the supply chain to prevent cyber threats.
By implementing a structured approach, organizations can significantly enhance their cybersecurity posture and protect their networks from potential vulnerabilities. Here’s how:
ISO 31000:2018 Compliance: Apply the risk assessment process as stated in ISO 31000:2018 to systematically manage supply chain risks.
ISO/IEC 27001 and 27002 Guidelines: Follow these standards for establishing, implementing, and maintaining robust information security management systems.
Regulatory Adherence: Ensure compliance with directive NIS2, which emphasizes supply chain cybersecurity.
Contractual Agreements: Include security requirements and vulnerability management expectations in supplier contracts.
Automate Monitoring Tools: Use AI and machine learning to detect anomalies. Leverage blockchain for transparent and tamper-proof tracking of goods and transactions.

Figure 13: Supply Chain Security Best Practice No. 4
5. Sustaining Ethical Practices and Managing Business Continuity
Integrating Sustainable Ethical Practices ensures a positive societal impact, whereas Business Continuity Management prepares an organization for disruptions and maintains critical operations during crises. Together, they create a resilient organization that is profitable and capable of thriving amid uncertainty and evolving risks. Here’s how:
ISO 9001:2015: Product Quality and Integrity
Implementing ISO 9001 verify that suppliers have effective quality management services leading to consistent, high-quality products reducing risk in the supply chain
ISO 20400:2017: Sustainable procurement
Implementing ISO 20400:2017 strengthens supply chain security by ensuring the quality and sustainability of products and practices among suppliers and service providers.
ISO 26000:2010: Social Responsibility
Encourages ethical sourcing, environmental stewardship, and considers social impacts in the supply chain.
ISO 22301:2019: Business Continuity Management
Reduces the risk of supply chain interruptions caused by quality or security issues, maintaining consistent operations.
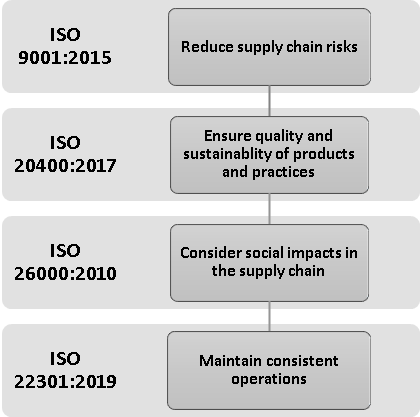
Figure 14: Supply Chain Security Best Practice No. 5
The Way Forward
Organizations must remain vigilant, agile, and forward-thinking to effectively counter emerging threats. By integrating best practices, leveraging cutting-edge technologies, and fostering strategic collaborations, businesses can ensure long-term security and resilience. As Gartner projects a 15% increase in cybersecurity spending, rising from $183.9 billion to $212 billion by 2025, the imperative to adapt is clear.
To overcome future supply chain challenges, companies must actively build resilience while addressing vulnerabilities in systems, processes, and capabilities.
Protecting your supply chain is more than just a necessity—it’s a strategic advantage. From thorough risk assessments to swift incident response, our comprehensive services are designed to keep your supply chain both secure and efficient. Our team of experts leverages cutting-edge technologies and industry-leading practices to build a robust, resilient supply chain tailored to your organization’s needs.
Ready to strengthen your supply chain security? Reach out to us today and learn how we can help you achieve long-term resilience and protection.
References:
- Admin. (2023, December 14). ISO 22301 – the Business Continuity Management Standard, simplified. ISMS.online. https://www.isms.online/iso-22301/
- BSI Group. (n.d.). Security Management for the Supply Chain (ISO 28000). BSI. https://www.bsigroup.com/en-IN/products-and-services/standards/iso-28000---security-management-for-the-supply-chain/
- Cyber Risk GmbH. (n.d.). European Cyber Resilience Act (CRA) - Regulation (EU) 2024/2847. https://www.european-cyber-resilience-act.com/
- Edwards, M. (2024, March 12). What is ISO/IEC 27001, The Information Security Standard. ISMS.online. https://www.isms.online/iso-27001/
- ISO. (2018). ISO 31000. International Organization for Standardization. https://www.iso.org/files/live/sites/isoorg/files/store/en/PUB100426.pdf
- ISO - ISO 26000 — Social responsibility. (2021, October 15). ISO. https://www.iso.org/iso-26000-social-responsibility.html
- [ISO 9001 in the supply chain]. (2015). In ISO 9001. https://www.iso.org/files/live/sites/isoorg/files/store/en/PUB100304.pdf
- ISO (International Organization for Standardization). (2017). ISO 20400 Sustainable procurement [Report]. ISO Central Secretariat. https://www.iso.org/files/live/sites/isoorg/files/store/en/ISO%2020400_Sustainable_procur.pdf
- Jessie. (2023, August 7). Supply chain security framework: S2C2F | CNCF. CNCF. https://www.cncf.io/blog/2023/08/04/supply-chain-security-framework-s2c2f/
- National Institute of Standards and Technology. (2022). C-SCRM fact sheet. In NIST Cybersecurity & Privacy Program. https://csrc.nist.gov/csrc/media/Projects/cyber-supply-chain-risk-management/documents/C-SCRM_Fact_Sheet.pdf
- NIS2 Directive: new rules on cybersecurity of network and information systems. (2025, January 15). Shaping Europe’s Digital Future. https://digital-strategy.ec.europa.eu/en/policies/nis2-directive
- Papaphilippou, M., Moulinos, K., Theocharidou, M., European Union Agency for Cybersecurity, & Siemens. (2023). GOOD PRACTICES FOR SUPPLY CHAIN CYBERSECURITY. https://www.enisa.europa.eu/sites/default/files/publications/Good%20Practices%20for%20Supply%20Chain%20Cybersecurity.pdf
- ReversingLabs. (2024, November 19). Cybersecurity Supply Chain Risk Management (C-SCRM) | ReversingLabs Glossary. ReversingLabs. https://www.reversinglabs.com/glossary/cybersecurity-supply-chain-risk-management-c-scrm
- Schirn, A. (2024, January 9). What is ISO 28000? The ANSI Blog. https://blog.ansi.org/?p=176875
- SCS 9001 - Supply Chain Security Management Standard. (n.d.). https://www.omnex.com/telecommunications/tia-scs-9001-training
- SCS 9001-Supply Chain Security Management System. (n.d.). DNV. https://www.dnv.in/services/scs-9001-supply-chain-security-management-system-224437/
- Security levels. (n.d.). SLSA. https://slsa.dev/spec/v0.1/levels
- Staff, I. (2024, May 14). Data sovereignty principles for the logistics and supply chain industries. InCountry. https://incountry.com/blog/data-sovereignty-principles-for-the-logistics-and-supply-chain-industries
- Strengthening and promoting innovation in the nation’s cybersecurity. (2025, January 17). Federal Register. https://www.federalregister.gov/documents/2025/01/17/2025-01470/strengthening-and-promoting-innovation-in-the-nations-cybersecurity
- Zacharoula. (2025, January 28). The Digital Operational Resilience Act (DORA) and Managing Third-Party Risk in the Supply Chain – Part 3. Eraneos. https://www.eraneos.com/articles/the-digital-operational-resilience-act-dora-and-managing-third-party-risk-in-the-supply-chain-part-3/
Advisory & Compliance Services
Audit & Assessment Services
Managed Security Services
Governance & Compliance Framework Development
Cyber Key Performance IndicatorsCISO Advisory
Advisory and Compliance ServicesStandard & Regulatory AdvisoryBusiness Continuity & Disaster Recovery PlanningIncident Response ReadinessData Privacy
Audit and Assessment Services
Cloud Security Assessment
Cyber Maturity Assessment
Privacy Impact Assessment
Red Teaming Service
VAPT
Managed Security Services
SOC as a Service
Third Party Risk Management
Vulnerability Management Services